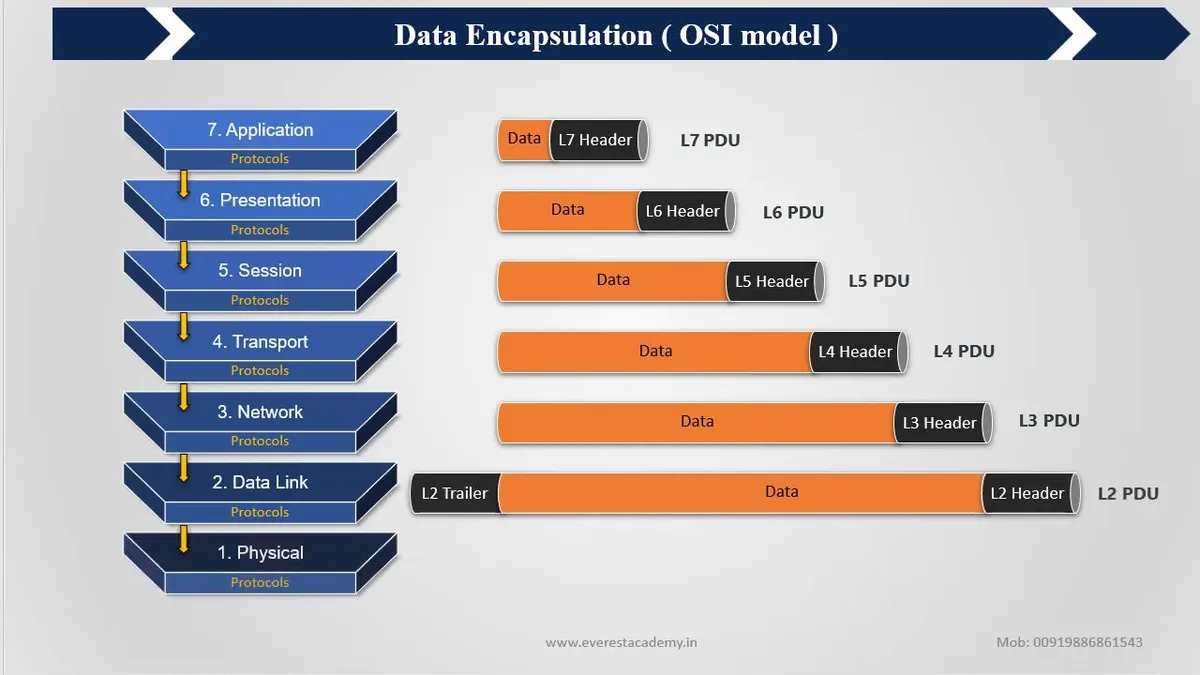
The OSI (Open Systems Interconnection) model was developed by the International Organization for Standardization (ISO) in the late 1970s and early 1980s. It was first published in 1984 as ISO 7498, and it provides a framework for understanding how different layers of a computer network interact with each other.
DOMAIN NAME SYSTEM
DNS, or Domain Name System, is the telephone book of the internet. It translates human-readable domain names, like www.example.com, into numerical IP addresses (192.168.8.10) that computers can understand and use to communicate with each other.
Slamm Technologies signs MoU with AmaliTech Ghana to equip students with digital employable skills.
Slamm Technologies Limited – a leading global Information Technology (IT) services provider – has partnered with AmaliTech Ghana Limited to provide employment opportunities and industry experience to young Ghanaians in the technology space.
DYNAMIC HOST CONFIGURATION PROTOCOL — DHCP
DHCP, or Dynamic Host Configuration Protocol, is like a superhero for your network! It takes care of automatically assigning IP addresses to all the devices connected to the network, just like how a superhero saves the day by solving all the problems. No more manual configuration, no more mistakes, and no more headaches!
TECHNIQUES USED IN CRYPTOGRAPHY Pt 1 — Encryption And Decryption
Today, we’ll be discussing techniques used in cryptography, which will help you understand how information is secured in today’s digital age. As a beginner in cybersecurity, understanding the various techniques used in cryptography is crucial for building a solid foundation in the field.
INTRODUCTION TO CYRPTOGRAPHY
At the beginner level, you will learn the basics of cryptography, such as the meaning of terms like algorithms, keys, and encryption. You’ll learn about different types of encryption methods, such as symmetric and asymmetric encryption, and their real-world applications.
IP ADDRESSING
TCP/IP is a protocol that requires a little bit of knowledge to configure the systems properly. When you configure TCP/IP, you must know the settings for the IP address, subnet mask, and default gateway. Let’s start with the IP address!
COMPARING CONTROL TYPES — How Organizations Can Manage Risk and Maintain the CIA of Their Assets.
Now, I know what you might be thinking — “What in the world is a security control?” Well, it’s basically a way to protect your information from bad guys who might try to access it without your permission.
CONTROL TYPES — Why It Is Important To An Organizations Information System
In our world, there are many things that we want to keep safe and secure. For example, we want to make sure our money is safe in the bank, our personal information is safe when we use the internet, and our schools and hospitals are protected from bad guys who might want to do harm.
Fundamentals Of Security
As the world becomes increasingly interconnected and reliant on technology, the importance of security in protecting sensitive information and assets has become more pronounced. At the core of any successful security program are the fundamental principles and practices that ensure the confidentiality, integrity, and availability of information and systems.